Flutter Security Best Practices 2026: 15 Ways to Protect Your App From Data Breaches
This guide covers 15 Flutter security best practices for 2026, including secure storage, SSL pinning, code obfuscation, API hardening, and penetration testing. Learn practical steps to protect user data, prevent breaches, and build Flutter apps that earn trust.
Summarise with AI
Short on time? Let AI do the work. Get the key points.
A fintech startup shipped its Flutter app last quarter. Three weeks later, attackers found an exposed API key in the source code. The result? Unauthorized access to payment data, a forced app store takedown, and months of damage control.
That story is not uncommon. And it is exactly why Flutter security can not be an afterthought.
Flutter gives you speed, a single codebase, and beautiful UIs across platforms. But speed without security is a liability. The same Dart code that compiles to native ARM also compiles your vulnerabilities into every build.
In 2025, the average cost of a mobile app security breach reached $6.99 million, according to a study commissioned by Guardsquare. The same research found that 62% of organizations experienced at least one mobile security incident, despite 93% believing their protections were sufficient. Android malware alone rose 67% year-over-year based on Zscaler 2025 data.
The reality is clear. If you are building with Flutter in 2026, security is your responsibility from the first line of code.
This guide walks you through 15 practical Flutter security best practices, organized from foundational habits to advanced protection layers. Each section includes what to do, why it matters, and how to implement it.
Let us get into it.
TL;DR
Flutter app security in 2026 requires a layered approach. This guide covers 15 best practices across storage, network security, code protection, and runtime defense. Avoid hardcoded secrets, use secure storage, validate inputs, and implement SSL pinning, encryption, and MFA. Security is not a one-time fix; it is an ongoing process built into every stage of development.
Table of Contents
Why Flutter App Security Matters More in 2026
Flutter powers apps for companies like Google Pay, BMW, and eBay. Its cross-platform efficiency and growing adoption also make it a bigger target for attackers.
Here is what the numbers look like right now.
App attacks surged to 83% according to Digital.ai’s 2025 report. Kaspersky blocked over 14 million mobile malware attacks in 2025. Banking trojans grew 1.5x year-over-year, with attackers diversifying delivery channels faster than ever.
Flutter compiles to native code, which helps with performance. But it does not automatically make your app secure. Insecure storage, hardcoded secrets, missing SSL pinning, and unvalidated inputs can turn any Flutter app into an easy target.
That is why businesses working with a professional Flutter app development company need to verify that security is built into the development process from the start, not patched in after launch.
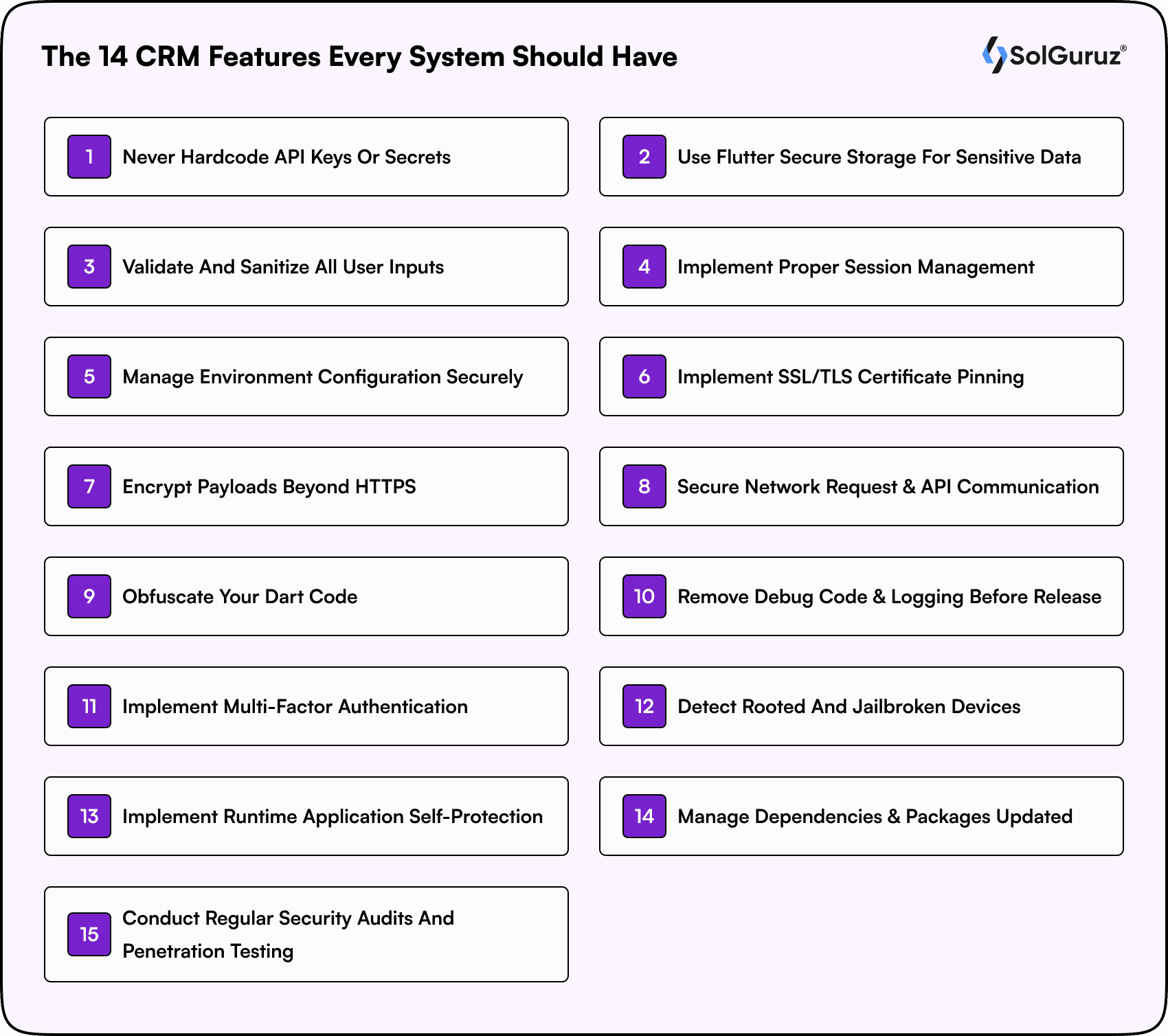
Foundation Layer: Core Security Practices Every Flutter App Needs
No matter how advanced your features are, security is what ultimately protects your users, your data, and your business reputation. Any reliable Flutter app development service prioritizes these foundational practices before scaling or shipping an app.
1. Never Hardcode API Keys or Secrets
This is the most common Flutter security mistake. Developers embed API keys, database credentials, or third-party service tokens directly in source code. Attackers can decompile your APK or IPA and extract those values in minutes.
What to do instead:
Use the dart-define flag to pass secrets at build time. This keeps sensitive values out of your codebase entirely. For local development, flutter_dotenv lets you load values from .env files that stay in .gitignore.
Also, restrict API key permissions through your provider’s dashboard. Limit keys by domain, IP, or specific API surfaces. Rotate keys on a regular schedule, quarterly at a minimum.
The principle is simple. If it is sensitive, it should never exist in your repository.
2. Use Flutter Secure Storage for Sensitive Data
SharedPreferences stores data as plain text. Anyone with physical or root access to the device can read it. For tokens, credentials, or any personally identifiable information, that is not acceptable.
flutter_secure_storage encrypts data using platform-native mechanisms. On Android, it uses the Keystore system with AES-256 encryption. On iOS, it uses the Keychain. This means sensitive data is protected by hardware-backed security on both platforms.
A few implementation tips that matter:
Set iOS Options with Keychain Accessibility. First unlock to control when stored data becomes available. On Android, use encryptedSharedPreferences: true for additional protection. Never store large datasets in secure storage since it is designed for small, high-sensitivity items like tokens and keys.
3. Validate and Sanitize All User Inputs
Client-side validation improves user experience. Server-side validation protects your application. You need both.
Every input field is a potential attack surface. Without proper sanitization, your app is open to SQL injection, cross-site scripting (XSS), and command injection attacks.
Use parameterized queries for any database interaction. Set maximum input lengths. Whitelist acceptable characters instead of trying to blacklist dangerous ones. Validate email formats, phone numbers, and any structured data against expected patterns.
The rule here is to never trust data coming from the client. Always validate on the server.
4. Implement Proper Session Management
Weak session handling is one of the top OWASP Mobile risks. If session tokens are predictable, never expire, or get stored insecurely, attackers can hijack user accounts without knowing any passwords.
Use short-lived access tokens (15 minutes is standard) paired with longer-lived refresh tokens. Store both in Flutter Secure Storage, never in SharedPreferences. Invalidate sessions on the server when users log out. Implement automatic session timeout after periods of inactivity.
For apps handling financial or health data, consider re-authenticating users before sensitive operations, even within an active session.
5. Manage Environment Configuration Securely
Different environments (development, staging, production) should have different configurations and different levels of access. Mixing them up is a common source of security incidents.
Use –dart-define to pass environment-specific values during the build process. Maintain separate Firebase projects or backend endpoints for each environment. Never ship debug configurations to production.
Double-check that debug logging, verbose error messages, and development-only API endpoints are completely removed before any production release.
Network Protection Layer: Securing Data in Transit
When your app communicates with servers, every request becomes a potential attack surface. A secure Flutter app development service ensures that data in transit is protected with multiple layers, not just basic HTTPS.
6. Implement SSL/TLS Certificate Pinning
HTTPS alone is not enough. Attackers can use fake or compromised certificates to perform man-in-the-middle attacks, intercepting data between your app and server. SSL pinning prevents this by verifying that your app only trusts a specific certificate or public key.
In Flutter, you can implement certificate pinning using the http_certificate_pinning package or by configuring a custom SecurityContext with Dart’s HttpClient. Pin against the public key hash rather than the full certificate, so you do not need to update the app every time the certificate renews.
Keep a backup pin in place for certificate rotation. Without one, a certificate renewal could lock all users out of your app.
7. Encrypt Payloads Beyond HTTPS
HTTPS encrypts the transport channel. But if your server is compromised, or if data needs to pass through intermediary services, transport encryption alone is not sufficient.
For high-value data like payment details, health records, or personally identifiable information, add application-layer encryption. Use AES-256 for payload encryption and RSA for secure key exchange.
The encrypt package in Dart supports AES and RSA operations. Generate unique encryption keys per session or per user rather than reusing a single key across your entire user base.
8. Secure Network Requests and API Communication
Every API call your app makes is a potential exposure point. Use HTTPS exclusively. Reject any HTTP connections. Set strict timeouts to prevent connection hanging. Add retry logic with exponential backoff, but cap the retries to prevent abuse.
Implement request signing so your backend can verify that requests genuinely come from your app and have not been tampered with. Use HMAC-SHA256 with a shared secret for signing.
On the Dio HTTP client (the most popular choice in Flutter), configure interceptors to automatically attach authorization headers, handle token refresh, and log network errors without exposing sensitive data.
Code Protection Layer: Defending Your Application Logic
Your application logic is one of your most valuable assets. Protecting it ensures that attackers cannot easily reverse engineer, exploit vulnerabilities, or understand how your system works internally.
9. Obfuscate Your Dart Code
Even though Flutter compiles Dart into native ARM code, it does not make your app immune to reverse engineering. Without obfuscation, class names, method names, and string literals remain readable, making it easier for attackers to analyze your app’s logic. That’s why teams that hire Flutter app developers often prioritize code obfuscation as a standard security step before release.
Use Flutter’s built-in obfuscation flags during the build process:
flutter build apk –obfuscate –split-debug-info=/<project-name>/debug-info
flutter build ios –obfuscate –split-debug-info=/<project-name>/debug-info
For Android, enable R8 full mode in gradle.properties with android.enableR8.fullMode=true for additional code shrinking and optimization.
Save the debug info directory securely. You will need it for crash report symbolication.
10. Remove Debug Code and Logging Before Release

Debug statements, verbose error messages, and development-only code paths can reveal internal architecture details to attackers. Things like database schema information in error logs, API endpoint patterns, or authentication flow details become free intelligence for anyone who decompiles your app.
Use Release Mode or Debug Mode flags from the Flutter foundation library to conditionally exclude debug code. Run a pre-release checklist that specifically scans for print statements, debugPrint calls, and any TODO/FIXME comments that might reference security-sensitive decisions.
11. Implement Multi-Factor Authentication
Passwords alone are not sufficient protection. According to Verizon’s Data Breach Investigations Report, stolen credentials remain the top initial attack vector year after year.
Build a layered authentication stack. Start with OAuth 2.0 or OpenID Connect for standard authorization flows. Add biometric authentication using Flutter’s local_auth package for fingerprint and Face ID support. Sensitive operations like large transactions or account changes require additional verification through OTP or authenticator apps.
Use short-lived JWT access tokens (15-minute expiration) paired with refresh tokens. Store both in flutter_secure_storage. Implement token rotation so that each refresh token can only be used once.
Runtime Protection Layer: Guarding Against Device-Level Threats
Even if your code and network are secure, the device itself can become the weakest link. Runtime protection ensures your app can detect and respond to threats in real time while it is actively running.
12. Detect Rooted and Jailbroken Devices
Rooted Android devices and jailbroken iPhones bypass platform security controls. On these devices, attackers can inspect app memory, modify runtime behavior, intercept network calls, and access data that would normally be protected by the OS sandbox.
Use packages like flutter_jailbreak_detection or safe_device to check device integrity at runtime. For apps handling financial data, consider restricting functionality or blocking access entirely on compromised devices.
Be transparent with users about why you are checking. A simple message explaining that the app detected a modified device and restricted access for security reasons goes a long way.
13. Implement Runtime Application Self-Protection (RASP)
Static security measures protect your app before it runs. RASP protects it while it is running. This includes detecting debugger attachments, code injection attempts, memory tampering, and hook frameworks like Frida.
According to the Guardsquare 2025 study, 60% of organizations have not implemented RASP. That is a significant gap given how accessible runtime attack tools have become.
While Flutter does not have a built-in RASP solution, third-party services like Guardsquare’s iXGuard and DexGuard, or Talsec’s freeRASP package for Flutter, can add runtime protection without major changes to your existing codebase.
Maintenance Layer: Keeping Security Current
Security is not a one-time effort; it is an ongoing process. Regular updates, monitoring, and testing ensure your app stays protected against newly discovered vulnerabilities and evolving attack methods.
14. Manage Dependencies and Keep Packages Updated

Every third-party package in your pubspec.yaml is a potential vulnerability. If a package maintainer’s account gets compromised, or if a package has an unpatched security flaw, your app inherits that risk.
Run flutter pub outdated monthly. Check package health scores on pub.dev. Review GitHub activity and issue responses before adopting new packages. Remove any unused dependencies since each one expands your attack surface.
Use dart pub global activate dependency_validator to identify packages listed in pubspec.yaml that are not actually used in your code.
For critical dependencies, pin specific versions and review changelogs before upgrading. Avoid blindly running Flutter pub upgrade without understanding what changed.
15. Conduct Regular Security Audits and Penetration Testing
Building securely is step one. Verifying that your app is secure is step two. Regular security audits catch issues that code reviews miss.
Use MobSF (Mobile Security Framework) for automated static and dynamic analysis. Run OWASP ZAP scans against your API endpoints. For deeper testing, use Frida for dynamic instrumentation and runtime analysis.
Quarterly automated scans should be the minimum. For apps in regulated industries like fintech or healthcare, add annual manual penetration tests conducted by external security specialists.
Keep detailed records of findings, remediation steps, and timelines. This documentation is valuable for compliance audits and for building a security culture within your development team.
Bonus: Backend API Security Checklist for Flutter Apps
Your Flutter app is only as secure as the backend it talks to. Even if your app-side security is flawless, an unprotected API endpoint can expose everything.
Here is what your backend security should include:
JWT tokens with short expiration (15 minutes for access tokens). Rate limiting at 100 requests per minute per IP as a baseline. Input validation on every endpoint without exception. Database encryption at rest. An API gateway with a Web Application Firewall (WAF) to filter malicious traffic. CORS configuration that only allows your specific app domains.
If your team does not have backend security expertise in-house, it is worth consulting with specialists. A single exposed endpoint can undermine months of careful app-side security work.
Building Flutter Apps That Earn Trust
Security is not a feature you add at the end. It is a discipline that runs through every sprint, every code review, and every deployment.
The 15 practices in this guide cover the full spectrum, from keeping secrets out of your codebase to detecting compromised devices at runtime. No single practice is sufficient on its own. Real security comes from layering these protections together.
Start with the foundation layer if you have not already. Audit your current storage approach, key management, and input validation. Then work upward through network protection, code hardening, runtime defenses, and ongoing maintenance.
At SolGuruz, our Flutter developers build security into every layer of the development process. We do not treat it as a checkbox. We treat it as a responsibility to the businesses and users who depend on the apps we build.
If you are ready to build a Flutter app that is fast, beautiful, and genuinely secure, talk to our team today.
FAQs
1. Is Flutter secure enough for enterprise and fintech apps?
Yes, when implemented correctly. Flutter for Enterprise App Development is widely adopted because it compiles to native code and integrates seamlessly with platform-level security features like Android Keystore and iOS Keychain. With proper implementation of obfuscation, SSL pinning, secure storage, and runtime protection (RASP), Flutter apps can meet enterprise-grade requirements and comply with standards like PCI-DSS.
2. What is flutter_secure_storage and how does it work?
flutter_secure_storage is a Flutter package that encrypts sensitive data using AES-256 encryption through Android Keystore and iOS Keychain. Unlike SharedPreferences which stores data in plain text, flutter_secure_storage protects tokens, credentials, and keys with hardware-backed encryption.
3. How do I protect API keys in a Flutter app?
Use the --dart-define flag to pass API keys at build time instead of hardcoding them. For local development, use flutter_dotenv with .env files added to .gitignore. Also restrict key permissions through your API provider's dashboard, limiting access by domain, IP, or API surface.
4. Do I need SSL pinning if my Flutter app already uses HTTPS?
Yes. HTTPS encrypts the transport layer, but attackers can still intercept traffic using compromised or fake certificates. SSL pinning verifies that your app only connects to your specific server certificate or public key, blocking man-in-the-middle attacks even on compromised networks.
5. How often should I run security audits on my Flutter app?
Run monthly dependency checks using Flutter pub outdated and automated scans with MobSF. Conduct quarterly security reviews of your codebase and API endpoints. For apps in regulated industries like fintech or healthcare, add an annual manual penetration test by external security specialists.
6. What is code obfuscation in Flutter, and why does it matter?
Code obfuscation renames classes, methods, and variables in your compiled code, making it much harder for attackers to reverse-engineer your app logic. Flutter supports obfuscation natively with the --obfuscate flag during builds. Without it, your compiled code retains readable names that reveal your app's architecture.
7. Can Flutter apps detect rooted or jailbroken devices?
Yes. Packages like flutter_jailbreak_detection and safe_device check for device integrity at runtime. For apps handling sensitive data, you can restrict functionality or display warnings when running on compromised devices where OS-level security controls have been bypassed.
8. What is RASP and does Flutter support it?
RASP (Runtime Application Self-Protection) monitors your app during execution to detect debugger attachments, code injection, and memory tampering. Flutter does not have built-in RASP, but third-party solutions like Talsec freeRASP for Flutter and Guardsquare provide runtime protection layers.
Megha Pithadiya is a Technical Lead (Mobile) at SolGuruz, bringing over 8 years of experience in mobile app development and technical leadership. Her work focuses on Android and cross-platform development, including Kotlin, Flutter, and React Native. She has led multiple mobile projects from architectural decisions through to production release. Across projects, Megha plays an active role in shaping mobile coding standards, architectural direction, and app performance optimizations. She also works closely with engineering teams, mentoring developers on clean architecture principles and building mobile codebases that are easier to maintain and scale.
From Insight to Action
Insights define intent. Execution defines results. Understand how we deliver with structure, collaborate through partnerships, and how our guidebooks help leaders make better product decisions.
Build Secure Flutter Apps With Confidence
Our Flutter developers bake security into every layer, from architecture to deployment. Get a free security review of your Flutter project.

Strict NDA

Trusted by Startups & Enterprises Worldwide

Flexible Engagement Models

1 Week Risk-Free Trial
Real-World Examples of Our Expertise
Explore how real-world challenges were turned into opportunities with our success stories and case studies, showcasing impactful solutions and measurable results.

AI Journaling App Development Solution
Discover with us how we built Dream Story, an AI-powered journaling application that helps manage daily notes by capturing your thoughts and emotions. A one-stop solution for those who love noting down daily summaries!
Generative AI
Prompt Engineering
AI Integration
Mobile App
Flutter
Android
iOS
Web App
Desktop
Website
UI/UX
Backend

Radon Mitigation System for Mitigators And Enterprise
SolGuruz designed and developed RadonSketch, a smart radon mitigation system solution for mitigators and enterprises. It modernizes outdated workflows with automation, guided compliance, and a powerful visual builder - built end-to-end by our expert team.
Real Estate
UI/UX
MVP Development
Mobile App
Flutter
Android
iOS
Backend
Launch & Maintenance
Digital Transformation
Digital Marketing